How Does Fraud Happen On Credit Cards
adminse
Apr 01, 2025 · 7 min read
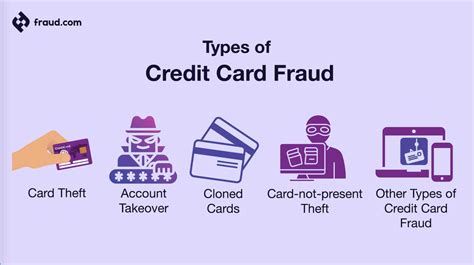
Table of Contents
How Does Credit Card Fraud Happen? Unmasking the Tricks and Traps
What if the seemingly secure world of credit cards is more vulnerable than we think? Credit card fraud is a pervasive threat, constantly evolving to exploit new technologies and human vulnerabilities.
Editor’s Note: This article on credit card fraud provides an up-to-date overview of the various methods employed by fraudsters, the latest prevention techniques, and what consumers can do to protect themselves. It draws on recent data and expert analysis to ensure accuracy and timeliness.
Why Credit Card Fraud Matters:
Credit card fraud impacts individuals, businesses, and the entire financial ecosystem. For individuals, it can lead to significant financial losses, damaged credit scores, and identity theft. Businesses bear the brunt of chargebacks and processing fees, impacting profitability and reputation. The financial industry invests heavily in security measures, yet the constant innovation by fraudsters necessitates continuous adaptation and improvement. Understanding the mechanics of credit card fraud is crucial for both prevention and mitigation.
Overview: What This Article Covers:
This article delves into the diverse landscape of credit card fraud, exploring its various methods, the underlying vulnerabilities exploited, and the preventative measures in place. We will examine both online and offline fraud tactics, the role of data breaches, and the evolving strategies employed by fraudsters. Furthermore, we'll analyze the implications for consumers and businesses and offer practical steps to minimize risk.
The Research and Effort Behind the Insights:
This article is the product of extensive research, drawing on reports from organizations like the Federal Trade Commission (FTC), the Consumer Financial Protection Bureau (CFPB), and leading cybersecurity firms. Data on fraud trends, successful prosecution cases, and advancements in fraud detection technology have been incorporated to provide a comprehensive and accurate analysis.
Key Takeaways:
- Understanding the Types of Credit Card Fraud: From skimming to phishing, we'll explore the diverse methods.
- The Role of Technology: How technology both facilitates and combats fraud.
- Prevention Strategies: What individuals and businesses can do to reduce their risk.
- The Future of Credit Card Fraud: Emerging threats and innovative prevention techniques.
Smooth Transition to the Core Discussion:
Now that we've established the significance of credit card fraud, let's dissect the methods criminals utilize to perpetrate these crimes.
Exploring the Key Aspects of Credit Card Fraud:
1. Definition and Core Concepts: Credit card fraud involves the unauthorized use of a credit card to make purchases or withdraw cash. This can involve stealing card information, creating counterfeit cards, or manipulating transaction systems. The core concept revolves around exploiting vulnerabilities in the payment system or human behavior.
2. Applications Across Industries: Credit card fraud is not confined to a single industry. It permeates e-commerce, brick-and-mortar retail, hospitality, and even the healthcare sector. Wherever credit cards are accepted, the potential for fraud exists.
3. Challenges and Solutions: The biggest challenge is the constant evolution of fraud tactics. As security measures improve, fraudsters adapt, employing sophisticated techniques to circumvent them. Solutions involve a multi-layered approach, combining technology, education, and robust legal frameworks.
4. Impact on Innovation: The fight against credit card fraud drives innovation in security technologies. This includes advancements in encryption, tokenization, biometric authentication, and fraud detection algorithms. This ongoing arms race between criminals and security professionals is constantly reshaping the payment landscape.
Credit Card Fraud Methods:
A. Card-Present Fraud (Offline):
- Skimming: This involves using a device to steal card information from the magnetic stripe or chip during a transaction. Skimmers are often attached to ATMs or point-of-sale (POS) terminals.
- Counterfeit Cards: Fraudsters create counterfeit cards using stolen card data. These cards can be used at any merchant that accepts credit cards.
- Card Cloning: This involves copying the information from a legitimate card onto a blank card. This is often done using specialized equipment.
- Shoulder Surfing: A simple yet effective method where criminals observe someone entering their PIN or credit card details.
- Physical Theft: This can involve stealing wallets, purses, or mail containing credit card information.
B. Card-Not-Present Fraud (Online):
- Phishing: Fraudsters send emails or text messages pretending to be legitimate organizations, tricking victims into revealing their card details.
- Malware: Malware installed on a computer can steal stored credit card information, login credentials, and other sensitive data.
- Data Breaches: Large-scale data breaches targeting businesses can expose millions of credit card numbers and other personal information.
- E-commerce Fraud: This involves using stolen credit card information to make purchases online. Often, fake accounts are created for this purpose.
- Man-in-the-Middle Attacks: Fraudsters intercept communication between a user and a website, stealing credit card information during the transaction.
C. Other Fraudulent Activities:
- Identity Theft: Credit card fraud often goes hand-in-hand with identity theft, where fraudsters use stolen personal information to open new accounts or apply for loans.
- Application Fraud: Fraudsters apply for credit cards using false identities or stolen information.
Exploring the Connection Between Data Breaches and Credit Card Fraud:
The relationship between data breaches and credit card fraud is undeniable. Large-scale data breaches, such as those targeting retailers or financial institutions, expose vast amounts of sensitive customer data, including credit card numbers, expiration dates, and CVV codes. This information is highly valuable to fraudsters and can be readily used to perpetrate card-not-present fraud on a massive scale.
Key Factors to Consider:
- Roles and Real-World Examples: The Target data breach of 2013 is a prime example of how a large-scale data breach can lead to widespread credit card fraud. Millions of credit card numbers were compromised, resulting in significant financial losses for both Target and its customers.
- Risks and Mitigations: The risk associated with data breaches is mitigated through robust security measures, such as encryption, intrusion detection systems, and regular security audits. Strong password policies and employee training are also vital.
- Impact and Implications: The impact of data breaches extends beyond financial losses. Reputational damage, legal liabilities, and regulatory penalties can significantly harm affected businesses. Consumers face the risk of identity theft and financial difficulties.
Conclusion: Reinforcing the Connection:
The link between data breaches and credit card fraud is a critical component of the overall fraud landscape. By strengthening security protocols and implementing effective data protection strategies, organizations can significantly reduce their vulnerability to breaches and the subsequent wave of fraudulent activity.
Further Analysis: Examining Data Breach Prevention in Greater Detail:
Data breach prevention requires a multifaceted approach, including strong network security, regular vulnerability assessments, employee training on security best practices, incident response planning, and robust data encryption. The implementation of multi-factor authentication (MFA) can also significantly reduce the success rate of phishing and credential-stuffing attacks.
FAQ Section: Answering Common Questions About Credit Card Fraud:
Q: What is the best way to protect myself from credit card fraud?
A: Regularly monitor your credit card statements, use strong passwords, be wary of suspicious emails and texts, and consider using fraud monitoring services.
Q: What should I do if I think my credit card has been compromised?
A: Immediately contact your credit card issuer to report the fraudulent activity and request a new card.
Practical Tips: Maximizing the Benefits of Fraud Prevention:
- Choose Strong Passwords: Use unique and complex passwords for all online accounts, including your banking and credit card portals.
- Enable Two-Factor Authentication (2FA): Whenever possible, enable 2FA on your online accounts to add an extra layer of security.
- Monitor Your Accounts Regularly: Check your credit card statements frequently for unauthorized transactions.
- Be Cautious of Phishing Attempts: Do not click on links or open attachments from unknown senders.
- Use Secure Wi-Fi: Avoid using public Wi-Fi for sensitive transactions.
- Keep Your Antivirus Software Up-to-Date: Ensure your computer is protected with updated antivirus and anti-malware software.
Final Conclusion: Wrapping Up with Lasting Insights:
Credit card fraud is a sophisticated and constantly evolving threat. Understanding the various methods used by fraudsters, and implementing proactive preventative measures, is crucial for protecting individuals and businesses alike. By staying informed, being vigilant, and utilizing the available security tools, you can significantly reduce your risk of becoming a victim of credit card fraud. The ongoing battle against this crime requires a collaborative effort between consumers, businesses, and law enforcement to ensure the security and integrity of the payment system.
Latest Posts
Latest Posts
-
What Is The Minimum Payment For A Discover Credit Card
Apr 04, 2025
-
What Is The Minimum Salary For A Credit Card In Kuwait
Apr 04, 2025
-
What Is The Minimum Amount For A Credit Card
Apr 04, 2025
-
What Is The Minimum Salary For A Credit Card In Qatar
Apr 04, 2025
-
What Is The Minimum Salary For A Credit Card In Pakistan
Apr 04, 2025
Related Post
Thank you for visiting our website which covers about How Does Fraud Happen On Credit Cards . We hope the information provided has been useful to you. Feel free to contact us if you have any questions or need further assistance. See you next time and don't miss to bookmark.